Developers mostly don't write in assembly. Instead, they write in higher-level languages, such as C or C++, and the compiler converts this high-level code into a low-level representation in assembly language. In this section, we will look at different code blocks represented in the assembly.
From assembly to high-level programming languages
Arithmetic statements
Now we will look at different C statements and how they are represented in the assembly. We will take Intel IA-32 as an example and the same concept applies to other assembly languages as well:
- X = 50 (assuming 0x00010000 is the address of the X variable in memory):
mov eax, 50
mov dword ptr [00010000h],eax
-
X = Y+50 (assuming 0x00010000 represents X and 0x00020000 represents Y):
mov eax, dword ptr [00020000h]
add eax, 50
mov dword ptr [00010000h],eax
- X = Y+ (50*2):
mov eax, dword ptr [00020000h]
push eax ;save Y for now
mov eax, 50 ;do the multiplication first
mov ebx,2
imul ebx ;the result is in edx:eax
mov ecx, eax
pop eax ;gets back Y value
add eax,ecx
mov dword ptr [00010000h],eax
- X = Y+ (50/2):
mov eax, dword ptr [00020000h]
push eax ;save Y for now
mov eax, 50
mov ebx,2
div ebx ;the result in eax, and the remainder is in edx
mov ecx, eax
pop eax
add eax,ecx
mov dword ptr [00010000h],eax
- X = Y+ (50 % 2) (% represents the remainder or the modulus):
mov eax, dword ptr [00020000h]
push eax ;save Y for now
mov eax, 50
mov ebx,2
div ebx ;the reminder is in edx
mov ecx, edx
pop eax
add eax,ecx
mov dword ptr [00010000h],eax
Hopefully, this explains how the compiler converts these arithmetic statements to assembly language.
If conditions
Basic If statements may look like this:
- If (X == 50) (assuming 0x0001000 represents the X variable):
mov eax, 50
cmp dword ptr [00010000h],eax
- If (X | 00001000b) (| represents the OR logical gate):
mov eax, 000001000b
test dword ptr [00010000h],eax
In order to understand the branching and flow redirection, let's take a look at the following diagram to see how it's manifested in pseudocode:
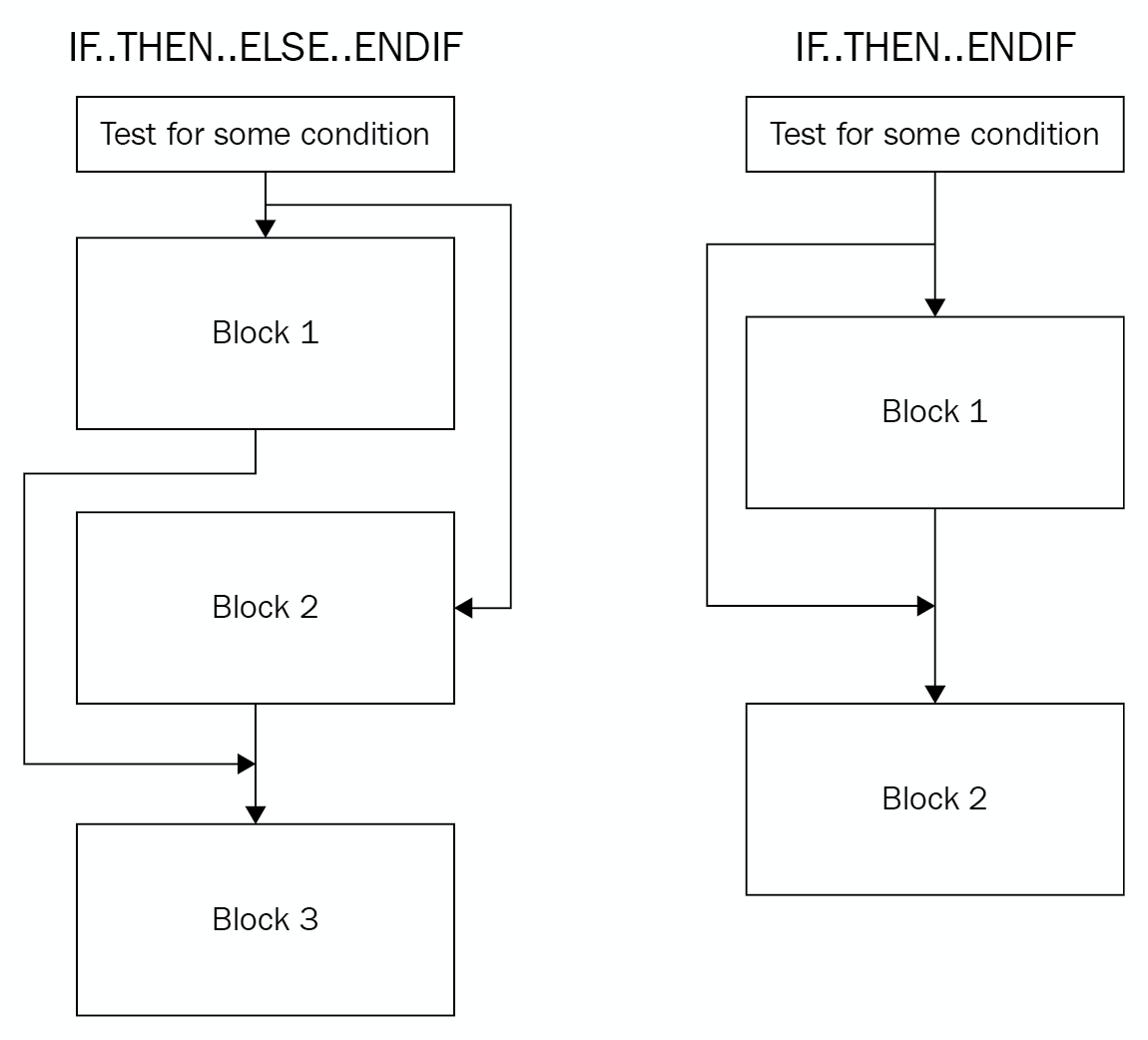
To apply this branching sequence in assembly, the compiler uses a mix of conditional and unconditional jmps, as follows:
- IF.. THEN.. ENDIF:
cmp dword ptr [00010000h],50
jnz 3rd_Block ; if not true
…
Some Code
…
3rd_Block:
Some code
- IF.. THEN.. ELSE.. ENDIF:
cmp dword ptr [00010000h],50
jnz Else_Block ; if not true
...
Some code
...
jmp 4th_Block ;Jump after Else
Else_Block:
...
Some code
...
4th_Block:
...
Some code
While loop conditions
The while loop conditions are quite similar to if conditions in terms of how they are represented in assembly:
|
While (X == 50){ |
1st_Block: |
|
Do{ |
1st_Block: |






































































