Databases in Metasploit
In Kali Linux, we will have to set up a database before we use the database functionality.
How to do it...
The following steps demonstrate the setting up of a database:
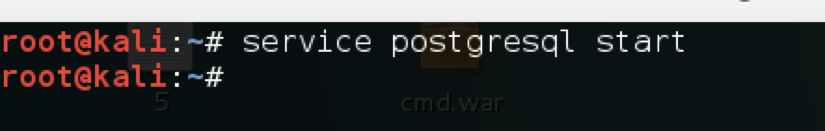
- First, we start the
postgresqlserver using the following command:
service postgresql startThe following screenshot shows the output of the preceding command:
- Then, we create the database and initialize it:
msfdb init- Once this is done, we load
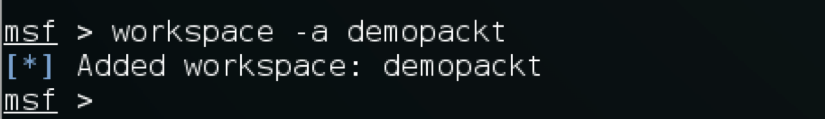
msfconsole. Now we can create and manage workspaces in Metasploit. A workspace can be considered a space where we can save all out Metasploit data with categorizations. To set up a new workspace, we use the following command:
workspace -a workspacenameThe following screenshot shows the output of the preceding command:
- To see all the commands related to the workspace, we can execute this:
workspace -h - Now that we have our database and workspace set up, we can use various commands to interact with the database.
- To import an existing Nmap scan into our database, we...