Methodology
Systematic and goal oriented penetration testing would always start with the right methodology. The following diagram provides the approach to any web application hacking, the methodology is divided into target selection, spider and enumeration, vulnerability scanning, exploitation, covering tracks, and maintaining access:
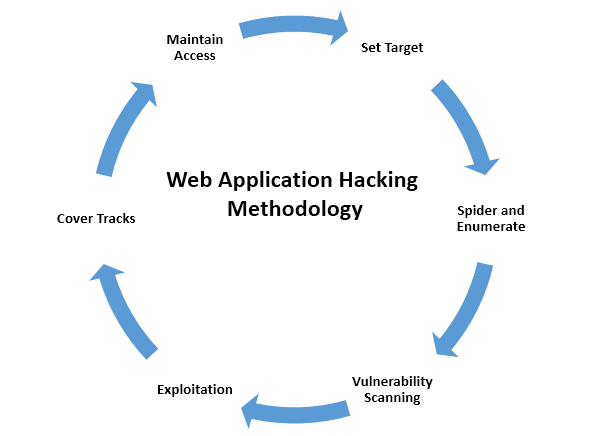
The preceding approaches are explained in detail as follows:
- Set Target: Setting the right target during a penetration test is very important, since attackers will focus more on specific vulnerable systems to gain system-level access as per the
Kill-chainmethod. - Spider and Enumerate: During this stage, attackers have already identified the list of web applications to dig deeper into specific vulnerabilities. Multiple methods are engaged to spider all the web pages, technology, and find everything relevant to advance into the next stage.
- Vulnerability Scanning: All the known vulnerabilities are collected during this phase against the well-known vulnerability databases...