Using Burp Suite to crawl a website
Burp is the most widely used tool for application security testing as it has functions that are similar to ZAP, with some distinctive features and an easy to use interface. Burp can do much more than just spidering a website, but for now, as a part of the reconnaissance phase, we will cover this feature.
Getting ready
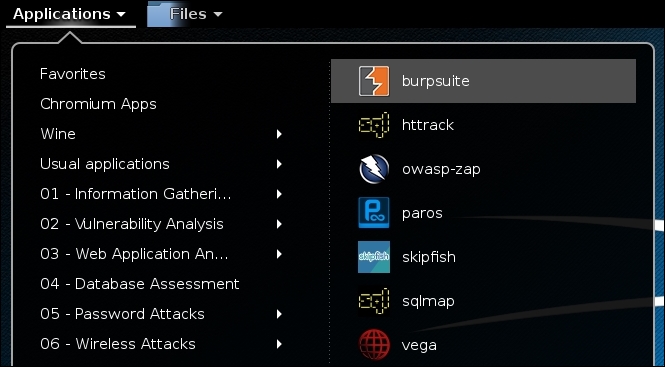
Start Burp Suite by going to Kali's Applications menu and then navigate to 03 Web Application Analysis | Web Application Proxies | burpsuite, as shown in the following screenshot:
Then, configure the browser to use it as a proxy through port 8080, as we did previously with ZAP.
How to do it...
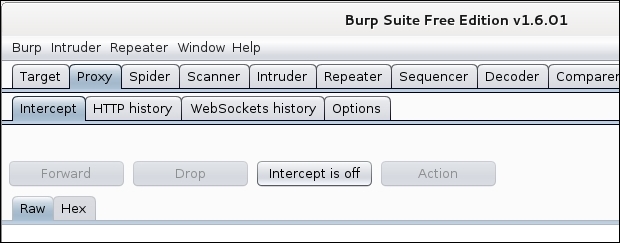
Burp's proxy is configured by default to intercept all requests. We need to disable it to browse without interruptions. Go to the Proxy tab and click on the Intercept is on button; it will change to Intercept is off, as shown:
Now, in the web browser, go to
http://192.168.56.102/bodgeit/.In Burp's window, when we go to the Target tab, we will see that it...
























































