Disabling username/password logins
One major role of a system administrator is to configure and manage users and groups on a Linux system. It also involves the task of checking the login capabilities for all users and disabling them if required.
Getting ready
All the steps given here have been tried on an Ubuntu system; however, you can follow these on any other Linux distribution also.
How to do it...
Here, we will discuss how the login capabilities of users can be restricted on a Linux system:
- We can restrict the access of a user account by changing the login shell of the account to a special value in the
/etc/passwdfile. Let's check the details of an account,user1as an example, in the/etc/passwdfile, as shown here:
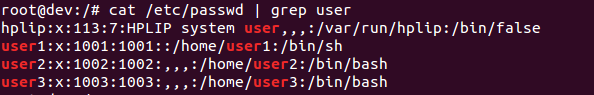
- In these details, the final value for the
user1account is set to/bin/bash. At present, we can log in from theuser1account. Now, if we want to change the shell of the user account we wish to restrict, we can do so as shown here:
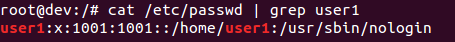
- If we try to log in from user 1 now, we get...