Access Management using IDAM
In today's world, a single Linux system may be used by various users locally or remotely. It becomes essential to manage the access of these users to protect sensitive and confidential information that should be accessible to only a few authenticated users.
IDAM, or Identity and Access Management, tools can help a system administrator to manage the identity and access of various users easily.
Getting ready
To get going with the installation and configuration of WSO2 Identity Server, we need any Linux distribution on which the Java environment is setup.
Here, we will see how to set up the Java environment:
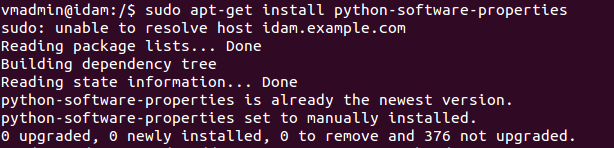
- Before installing the JDK, we shall install a package related to Python as part of the dependency. The command to do this is as follows:
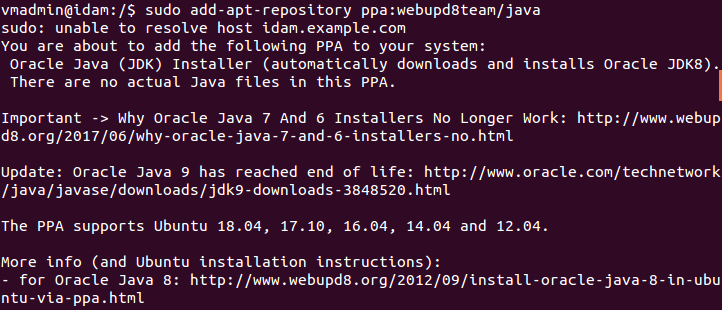
- Now, to install Oracle JDK, the official version distributed by Oracle, we will have to update the system's package repository and add Oracle's PPA. To do this, we run the following command:
- Now, install the stable version of Java...