Exploring Guymager
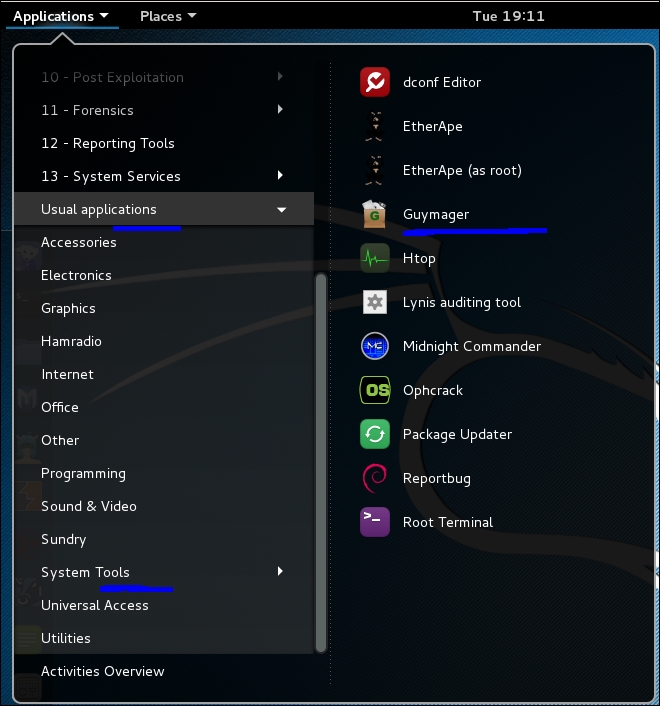
On most forensic projects, you will work from an image, so first let's get an image to work with. Guymager is a forensic imager for media acquisition. It has a nice GUI and saves images out in several formats used in forensic imaging. The application will also make a clone of a drive. You can find Guymager in the Usual applications | System Tools menu:
Guymager has two modes of saving files:
The acquire mode, where you might want an image for digital evidence.
The clone mode, in case you need the entire partition duplicated.
The difference is, in acquire mode the image is digitally signed with a checksum and other information to prove no tampering of the evidence has been done to the image. In a legal case, you would pull two images. You would acquire one and digitally sign it for evidence and clone another to investigate. Since you really never know whether your case could become part of a legal proceeding, you might want to always pull two copies of the partitions you are...