Configuring and using the TCP Wrapper
Securing a server by restricting access is a critical measure, which should never be avoided while setting up a server. Using TCP Wrappers, we can allow only those networks to have access to our server's services that we have configured and support TCP Wrappers.
Getting Ready
To demonstrate these steps, we use two systems that are on the same network and can ping each other successfully. One system will be used as the server and the other as the client.
How to do it?
Linux provides several tools to control access to network services. TCP Wrappers is one among those and adds an additional layer of protection. Here, we will take a look at how to configure TCP Wrappers to define access for different hosts.
First, we need to check whether a program supports TCP Wrappers or not. To do this, first find the path of an executable program using the
whichcommand:which sshd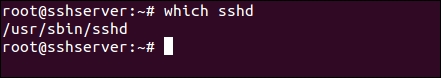
Here, we have used the SSH program as an example.
Next, we use the
lddprogram to check the compatibility...