Configuring a console for debugging using Netconsole
If we want to capture a kernel panic, it becomes hard once the system has been rebooted as there are no logs created for this. To solve this issue, we can use Netconsole.
A kernel module helps by logging kernel print messages over UDP. This becomes helpful with debugging problems when logging on to the disk fails.
Getting ready
Before starting the configuration of Netconsole, we need to know the MAC address of the system where the UDP packets will be sent. This system is referred to as a receiver, and it may be in the same subnet or a different one. These two cases are described here:
The first case is when the receiver is in the same subnet.
The IP address of the receiver in this example is
192.168.1.4. We will send UDP packets to this IP address.
Now, let's find the MAC address of the receiver system by executing this command. In the following case, the IP address is of the receiver system.
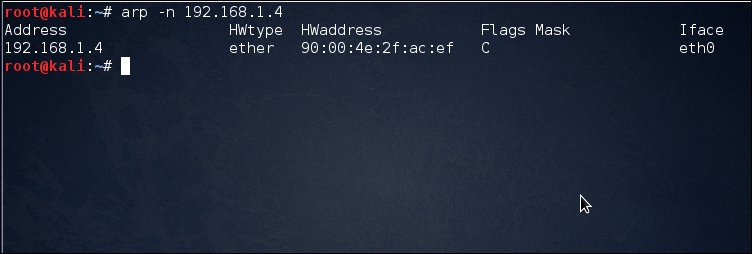
As we can see in the preceding example,
90:00:4e:2f...