Setting up a Kerberos server with Ubuntu
Kerberos is an authentication protocol for allowing secure authentication over untrusted networks by using secret-key cryptography and trusted third parties.
Getting ready
To get Kerberos set up and running, we need three Linux systems (in our example, we have used Ubuntu). They should be able to communicate with each other and they should also have accurate system clocks.
We have given the hostname to each system as mentioned here:
Kerberos system:
mykerberos.comSSH Server system:
sshserver.comClient system:
sshclient.com
After doing this, edit the /etc/hosts file in each system and add the following details:
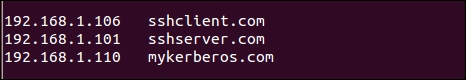
The IP address and the hostname can be different for your systems. Just make sure that after doing these changes they can still ping with each other.
How to do it...
Now, let's see how to complete the setup of the Kerberos server and the other systems for our example.
The first step is to install the Kerberos server. To do this, we will run the given...