Parsing SQLite databases with SQLite Wizard
The UFED program has already been described previously in Chapter 4, Windows Phones and BlackBerry Acquisition. This program has the SQLite Wizard module, which can be used for data extraction from SQLite databases.
Getting ready
Unfortunately, the SQLite Wizard module cannot be started individually, and before using it, an expert has to analyze extracted data from a mobile device via UFED Physical Analyzer. When the analysis is done, click the category:
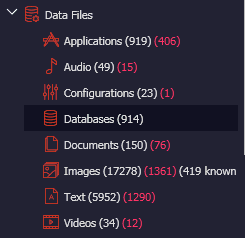
Databases category
In the main window of the program, the tab will be displayed that contains information about SQLite databases extracted from the examined mobile device. The window will also display information on whether the database was analyzed via UFED Physical Analyzer or not:
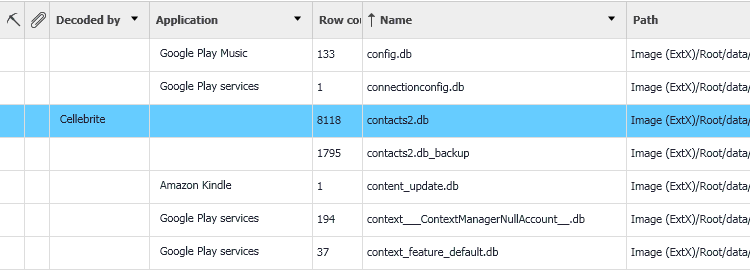
Information about databases displayed in the main window of UFED Physical Analyzer
Viewing this window, an expert will face an unpleasant discovery. It turns out that most of the extracted SQLite databases cannot be analyzed...