4. Patching Binary Using IDA
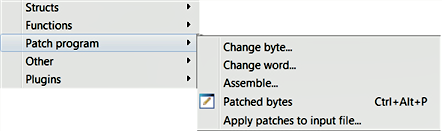
When performing malware analysis, you may want to modify the binary to change its inner workings or reverse its logic to suit your needs. Using IDA, it is possible to modify the data or instructions of a program. You can perform patching by selecting Edit| Patch program menu, as shown in the following screenshot. Using the submenu items, you can modify a byte, word, or assembly instructions. A point to remember is that when you are using these menu options on the binary, you are not really modifying the binary; the modification is made to the IDA database. To apply the modification to the original binary, you need to use the Apply patches to input file submenu item:
4.1 Patching Program Bytes
Consider the code excerpt from the 32-bit malware DLL (TDSS rootkit), which is performing a check to make sure that it is running under spoolsv.exe. This check is performed using string comparison at ➊; if the string comparison fails, then the code jumps to end of the function...

































































