Firewall identification with Metasploit
Metasploit has a scanning auxiliary module that can be used to perform multithreaded analysis of network ports to determine whether those ports are filtered, based on SYN/ACK probe-response analysis.
Getting ready
To use Metasploit to perform firewall identification, you will need to have a remote system that is running network services. Additionally, you will need to implement some type of filtering mechanism. This can be done with an independent firewall device or with host-based filtering such as Windows Firewall. By manipulating the filtering settings on the firewall device, you should be able to modify the results of the scans.
How to do it…
Let's use Metasploit to perform firewall identification:
- To use the Metasploit ACK scan module to perform firewall and filtering identification, you must first launch the MSF console from a Terminal in Kali Linux and then select the desired
auxiliarymodule with theusecommand:
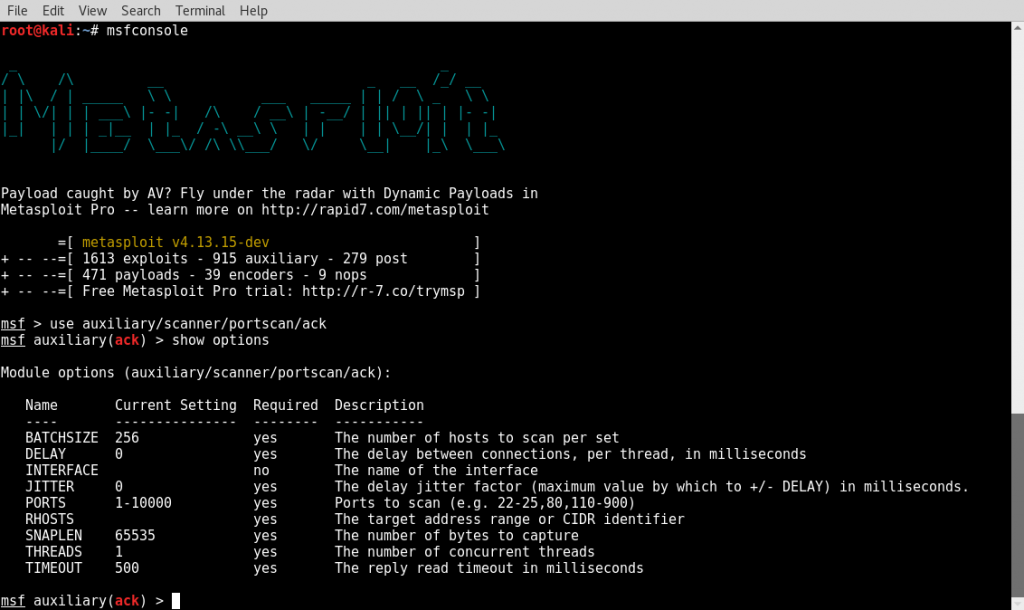
- Once the module has been selected...