Elements of enterprise security
The IT security of an enterprise has multiple dimensions, ranging from protecting data, to preventing denial of service attacks, to defending against ransomware attacks and the spread of viruses and worms. All these dimensions need to be taken care of while creating a security architecture for the enterprise. Security is like a complex problem that can be handled if broken into its constituent elements. To this end of breaking the security problem into its elements, we will describe a layered model of the IT assets and what needs to be protected.
The following figure shows a layered model of the enterprise IT assets:
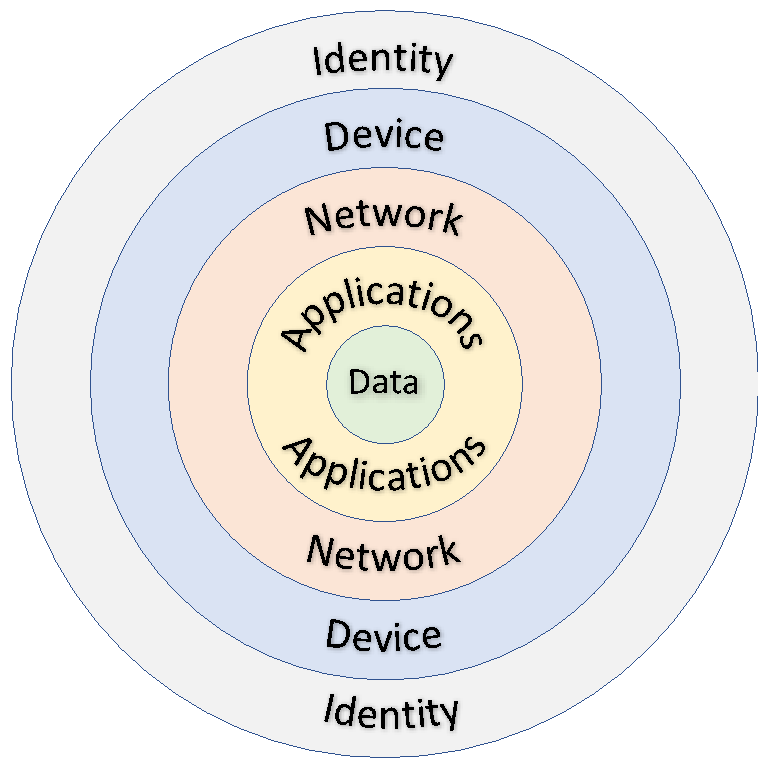
Figure 1: A layered approach to security
The ultimate goal of the organization is to protect its data. This data could be customer data, intellectual property, bank record information, or any other data that is of value to the organization or the loss of which can cause a loss of reputation. Data is protected using technologies on the perimeter systems...