Security Fundamentals
The fundamentals of security are the foundation of protecting our assets, and there must be a strategy or methodology that we adapt for security. This is the CIA triad; let's look at its breakdown.
CIA Triad Concept
Most security books start with the basics of security by featuring the CIA triad—this is a conceptual model designed to help those writing information security policies within an organization. It is a widely used security model and it stands for confidentiality, integrity, and availability, the three key principles that should be used to guarantee you have a secure system:
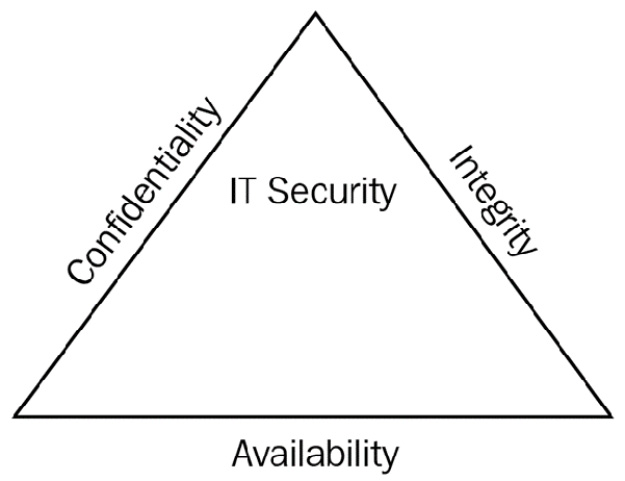
Figure 1.1 – CIA triad
We'll discuss these principles in more depth here:
- Confidentiality: Prevents the disclosure of data to unauthorized people so that only authorized people have access to data. This is known as the need-to-know basis. Only those who should know the contents should be given access. An example would be that your medical history is only available to your doctor and nobody else.
We also tend to encrypt data to keep it confidential. There are two types of encryption, known as symmetric and asymmetric. Symmetric encryption uses one key, known as the private key or shared key. Asymmetric encryption uses two keys, known as the private key and the public key.
- Integrity: This means that you know that data has not been altered or tampered with. We use a technique called hashing that takes the data and converts it into a numerical value called a hash or message digest. When you suspect changes have taken place, you would check the hash value against the original. If the hash value has changed, then the data has been tampered with. Common hashing algorithms covered in the exam are Secure Hash Algorithm Version 1 (SHA1) 160-bit, SHA2 256-bit, SHA3 512-bit, and Message Digest Version 5 (MD5) 128-bit. SHA1 is more secure than MD5; however, MD5 is faster. The higher the number of bits, the more secure, and the lower the number, the faster it is.
- Availability: Availability ensures that data is always available; an example would be if you wanted to purchase an airplane ticket and the system came back with an error saying that you could not purchase it. This could be frustrating and hence, availability is important. Examples of availability could be using Redundant Array of Independent Disks (RAID), maybe a fail-over cluster, a data backup, or Heating Ventilation Air Conditioning (HVAC) to regulate the system for critical servers.
Least Privilege
Least Privilege is where you give someone only the most limited access required so that they can perform their job role; this is known as a need-to-know basis. The company will write a least privilege policy so that the administrators know how to manage it.
Defense in Depth Model
Defense in Depth is the concept of protecting a company's data with a series of protective layers so that if one layer fails, another layer will already be in place to thwart an attack. We start with our data, then we encrypt it to protect it:
- The data is stored on a server.
- The data has file permissions.
- The data is encrypted.
- The data is in a secure area of the building.
- There is a security guard at the building entrance checking identification.
- There is CCTV around the perimeter.
- There is a high fence around the perimeter.
Let's look at this from the intruder's perspective, trying to jump the fence, and see how many layers they have to circumvent:
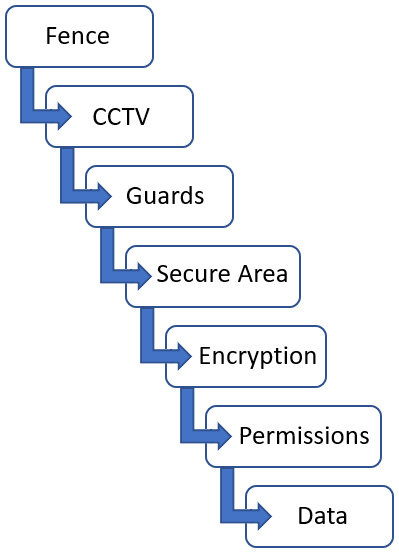
Figure 1.2 – Defense in Depth model
Let's now compare the different control types.