Importing TCP server/ browser-based exploits into Metasploit
In the following section, we will see how we can import browser based or TCP server based exploits in Metasploit.
During an application test or a penetration test, we might encounter software that may fail to parse data from a request/response and end up crashing. Let us see an example of an application that has vulnerability when parsing data:
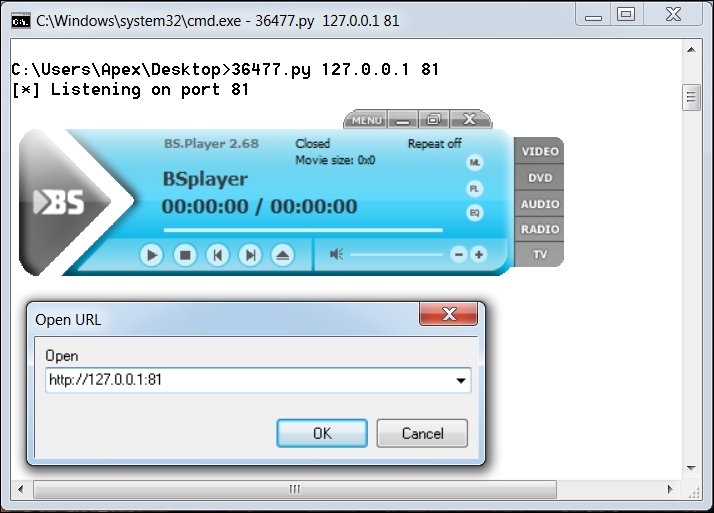
The application used in this example is BSplayer 2.68. We can see we have a Python exploit listening on port 81. The vulnerability lies in parsing the remote server's response; when a user tries to play a video from a URL. Let us see what happens when we try to stream content from our listener on port 81:
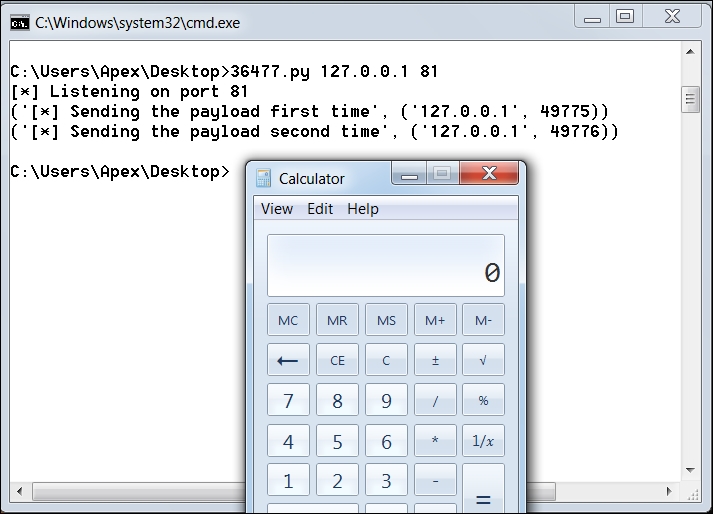
We can see the calculator application popping up, which denotes the successful working of the exploit.
Note
Download the Python exploit for BSplayer 2.68 from https://www.exploit-db.com/exploits/36477/
Let us see the exploit code and gather essential information from it in order to build...