Acquiring memory using FTK Imager
Memory is a very important source of evidence in an investigation process. All activities that happen on a system are usually reflected in the memory at the time.
The following is a step-by-step guide to acquire a system's volatile memory using the product FTK Imager.
This can be downloaded for free at http://accessdata.com/product-download.
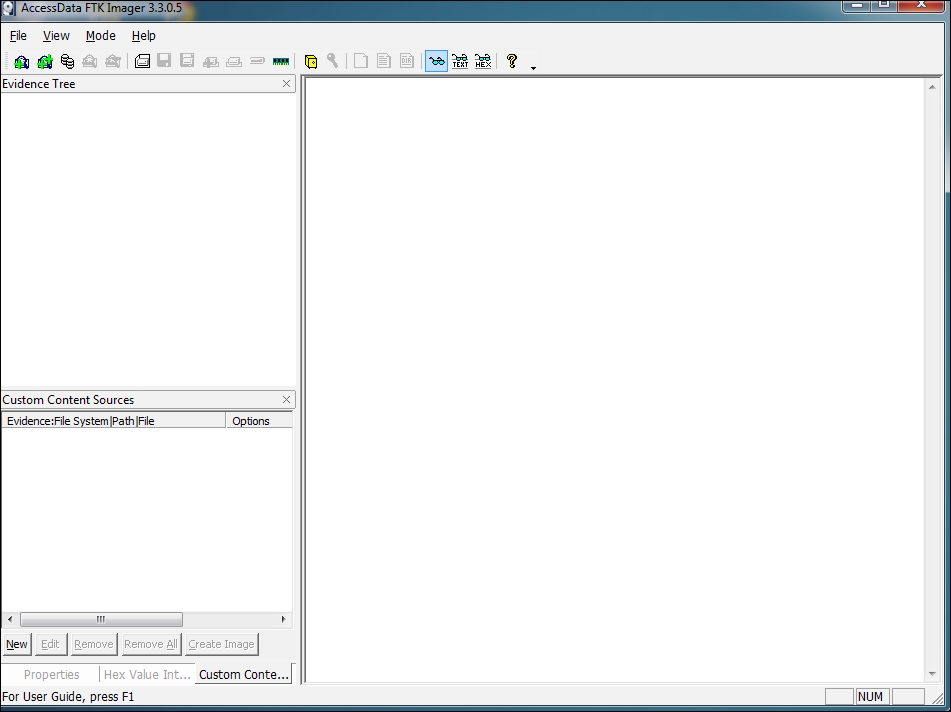
Run FTK Imager as an administrator, as shown in the following screenshot:
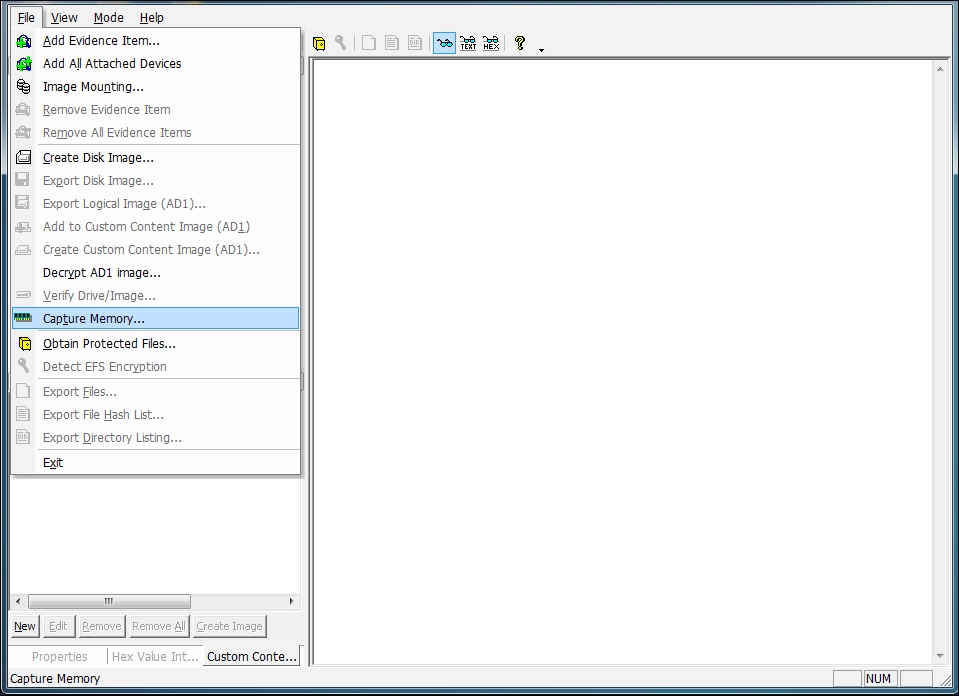
Click on the File menu and select Capture Memory, as shown in the following screenshot:
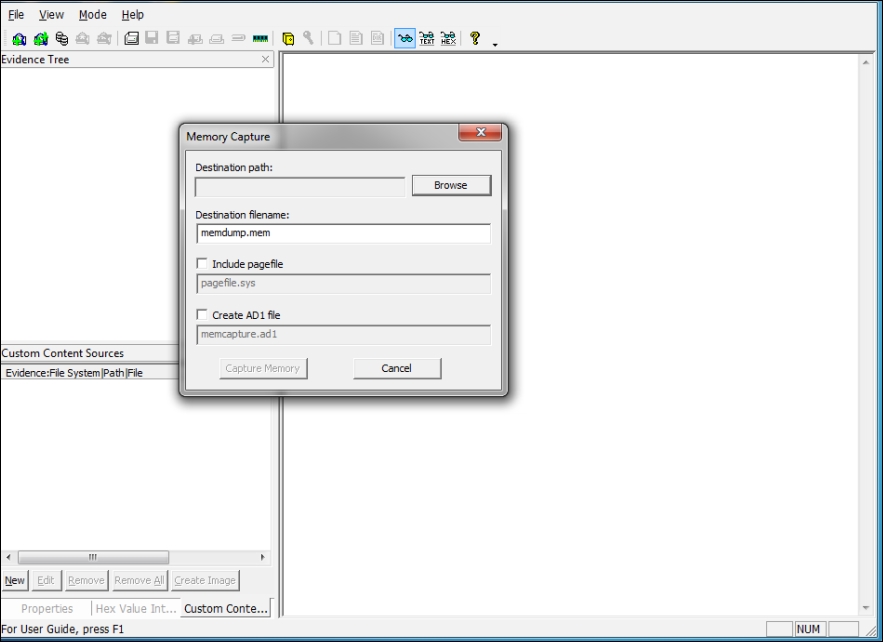
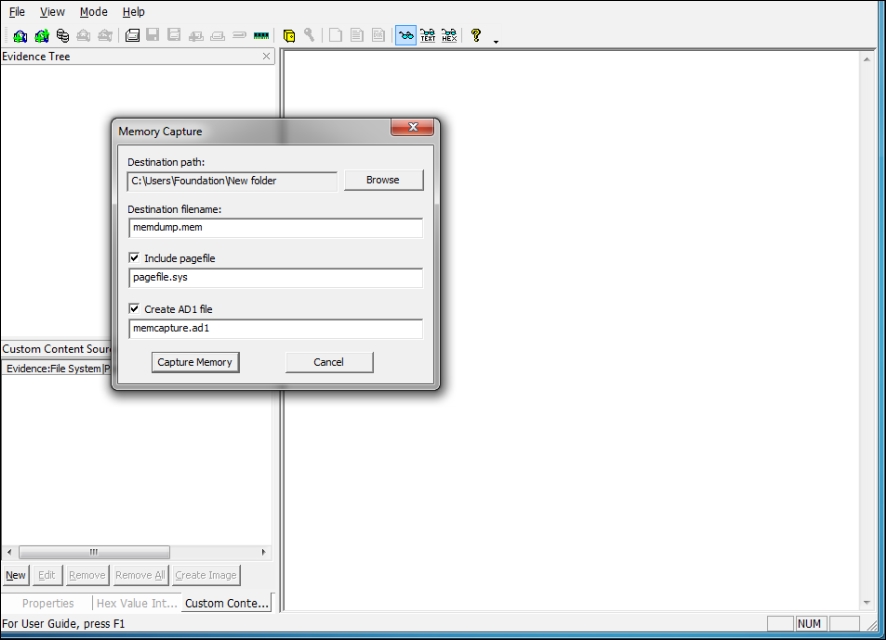
Browse the destination folder, where you want to save the acquired memory dump, as shown in the following screenshot:
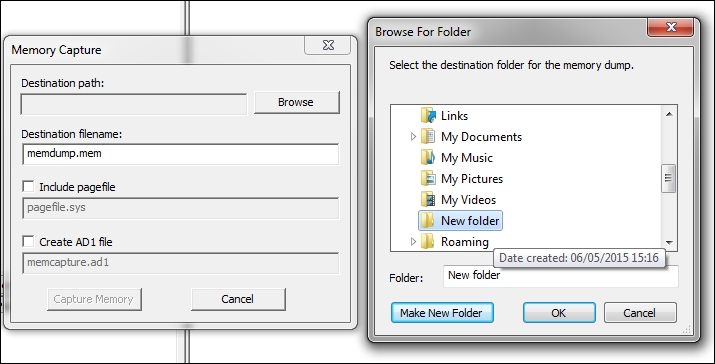
Click on Browse and create a destination folder, as shown in the following screenshot:
After creating the destination folder, click on Capture Memory, as shown in the following screenshot:
Click on Capture Memory and the memory dumping will start, as shown in the following screenshot:
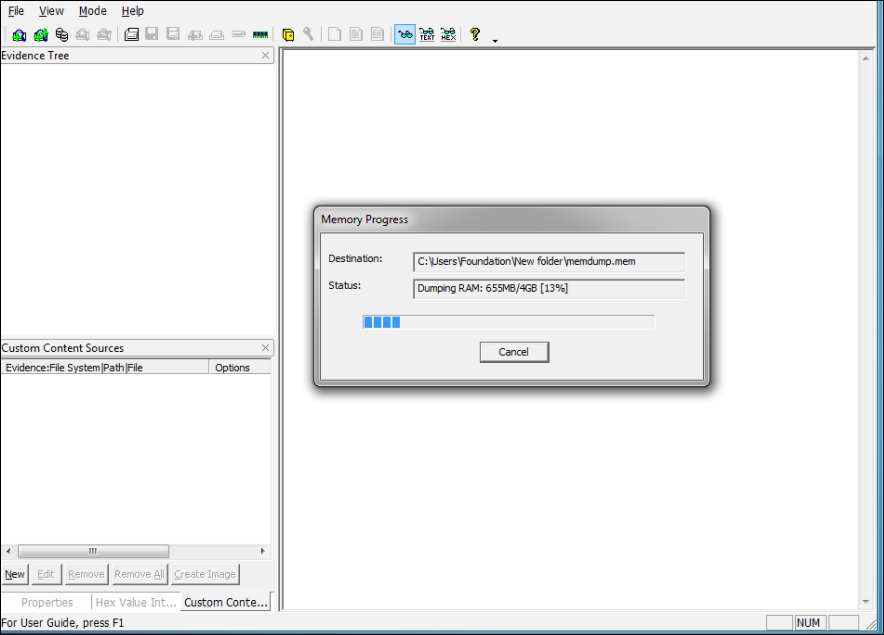
Creation of pagefile starts after the completion of memory dump,...

























































