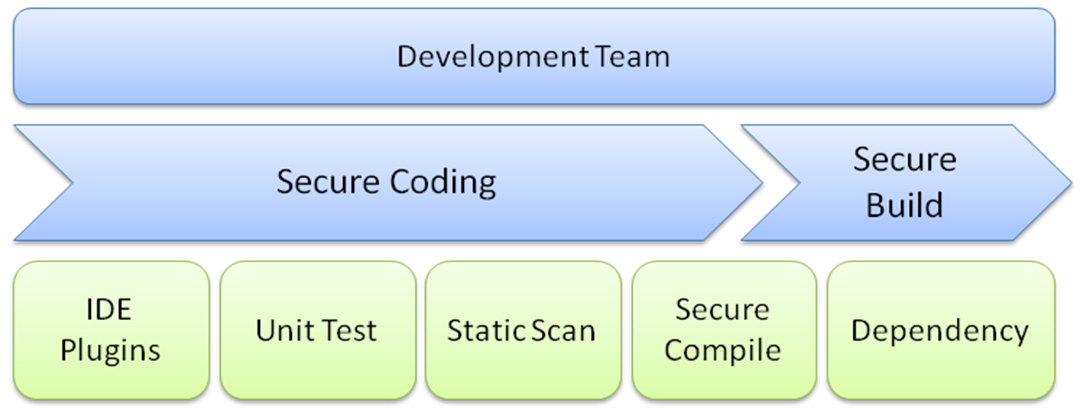
Security practices in development
The security practices of the development team consist of secure coding and secure build delivery. For the secure coding, we can have an IDE plugin do the code scanning, or we can also require security unit testing and run a static code scan of the whole project. For the secure build delivery, we need to ensure that the compiler options are configured properly and review all the dependency components for known vulnerabilities. The following diagram shows the overall security practices we can plan into the development stage. We will introduce some of the open source security tools and practices for these security activities in the upcoming sections:
IDE plugins to automate the code review
The key advantages of using the IDE plugins to perform the automated security code review is that the tools can provide informative suggestions for fixes during the coding stage. It works in a similar way to a spellchecker. This will reduce lots of code review efforts and...