Paramiko
Running commands in remote systems via SSH is one of the most common components of automation. The Python module paramiko makes this easy by providing a programmatic interface to SSH. Paramiko gives you an easy way to use SSH functions in Python through an imported library. This allows us to drive SSH tasks, which you would normally perform manually.
Establish SSH connection with paramiko
The main class of paramiko is paramiko.SSHClient, which provides a basic interface to initiate server connections:
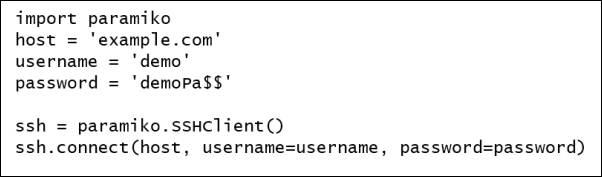
This will create a new SSHClient instance, and we then call the connect() method, which connects to the SSH server.
When we connect to a remote machine with any SSH client, that remote host's key will be automatically stored in the .ssh/known_hosts file in our home directory. So, the first time we connect to a remote system, we will get a message, as follows:
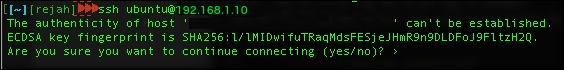
When you type yes for this message, it will add an entry in the known_hosts file. By accepting this message, a level of trust is...