Fake OS-signature reply to nmap
In this section, we are going to create a fake OS signature. By using the following nmap, we can identify the OS of the victim machine:
nmap -O <ip-address>: The nmap sends seven TCP/IP-crafted packets and evaluates the response with its own OS signature databases. For more details, you can read the web page at https://nmap.org/misc/defeat-nmap-osdetect.html.
The nmap needs at least one open and one closed port to identify the OS. Again, we are going to use all the previous codes. The ports 445 and 135 acts as open ports and 80 act as a closed port.
Let's run nmap as shown in the following screenshot:
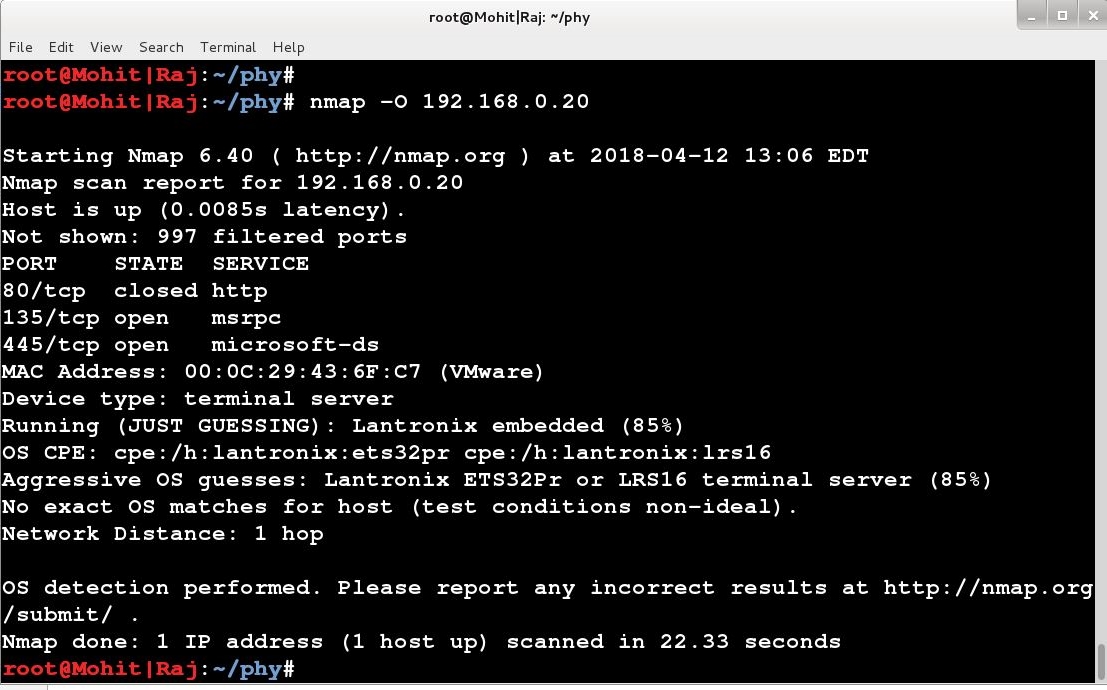
It is giving a different OS, not Debian. You can make the code more complicated by learning the nmap OS detection algorithm.