Brute force password hashes
In this recipe, we will crack hashes using John the Ripper in brute force mode. We will work with a local shadow file from a Linux machine and we will try to recover passwords by brute forcing them.
Getting ready
Let's ensure the following prerequisites:
- Your Kali machine is powered up
- You have some sample users and passwords setup on your Linux machine add some more and make a couple accounts with random 4 character passwords.
- You copied the
shadowfile to your Kalirootdirectory
How to do it...
We will use a brute force method of attack on password hashes:
- Verify you have the
shadowfile copied in therootdirectory:
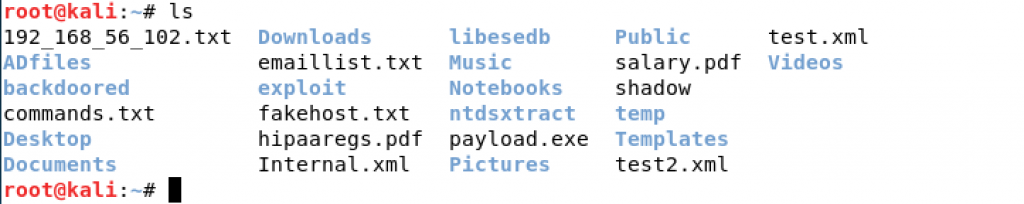
Directory listing
- To use a brute force attack against our
shadowfile we can use the following commands. This command will take a very long time to crack any passwords and is considered as a last resort:
cd john -incremental:lanman shadow
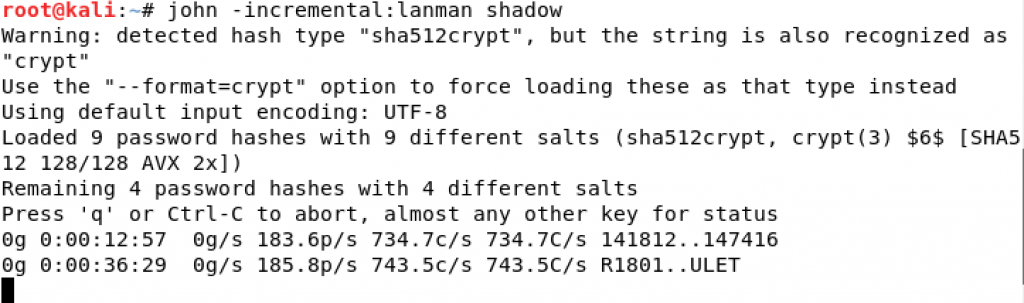
John the Ripper progress screen
Note
You can press the spacebar at any time to get an update as to how the password cracking...