Digging deep with theharvester
The theharvester tool is a great tool for penetration testing as it helps us find a lot of information about a company. It can be used to find email accounts, subdomains, and so on. In this recipe, we will learn how to use it to discover data.
How to do it...
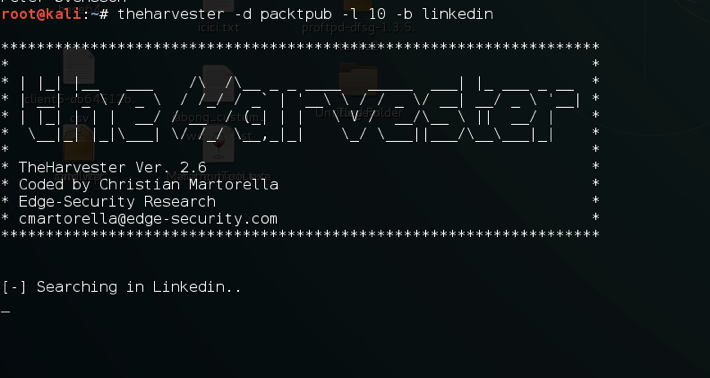
The command is pretty simple:
theharvester -d domain/name -l 20 -b all The following screenshot shows the output of the preceding command:
How it works...
In the preceding recipe, -d is for the domain name or the keyword we want to search, -l is for limiting the number of search results, and -b is the source we want the tool to use while gathering information. The tool supports Google, Google CSE, Bing, Bing API, PGP, LinkedIn, Google Profiles, people123, Jigsaw, Twitter, and Google Plus sources.